Beware of the Google Chrome ‘Missing Font’ Hack
PLEASE NOTE: EMSISOFT USERS ARE PROTECTED FROM THIS HACK.
This week a very well executed malware attack aimed at users who visit compromised web sites was found by Mahmoud Al-Qudsi of NeoSmart Technologies. The hack tries to trick users into believing the reason why the font on the page they’re visiting is garbled and unreadable, is because the their PC is missing a font.
Before we post the article that explains this hack, let us warn you that no site is going to warn you that you’re missing a font. The way Web sites work is – if a site uses a font that is not installed on your PC, you’ll see the site’s font in whatever your default font is – you won’t see a garbled, unreadable mess.
So DO NOT FALL FOR THIS TRICK. Your PC will be infected. Here’s what it looks like so you’ll know it if you see it.
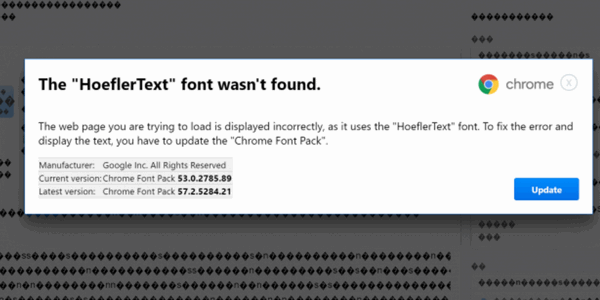
Notice how the text on the compromised web site is garbled and unreadable.
Here’s a close up:
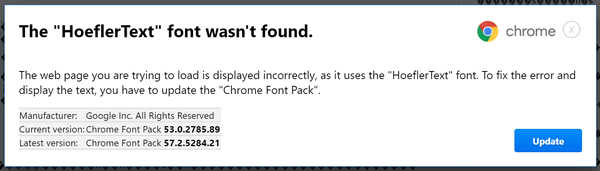
DO NOT CLICK “UPDATE”. Close the page or your browser immediately.
As of today ( 23 February 2017) there has been no patch for Chrome released by Google. Google has been notified and hopefully Chrome will be patched against this hack soon.
Here’s an article from ItPro written by Dale Walker, with more detailed information about the “missing font” hack:
Chrome malware masquerades as ‘missing font’ files
The infection was first spotted on an unnamed WordPress website by Mahmoud Al-Qudsi, a researcher at cybersecurity firm NeoSmart Technologies, who detailed the process in a blog post.
The attack involves a hacker exploiting JavaScript to alter the rendering of content on a webpage, causing it to resemble mis-encoded text which appears as a jumble of symbols and shapes. The code then prompts the user to download the missing fonts through a Chrome language pack to decipher the text.
Clicking “Update” results in a file called “Chrome Font v7.5.1.exe” being downloaded and a second prompt encourages the user to run the file, all the while appearing as a perfectly safe Chrome download.
The attack is particularly well disguised and makes every attempt to appear a legitimate Chrome pop up, including the correct text formatting and right use of colours for the “Update” button.
“This attack gets a lot of things right that many others fail at,” said Al-Qudsi. “The premise is actually believable: the text doesn’t render, and it says that it is caused by a missing font (Hoefler Text, which is a real font), which it then prompts you to download and install.”
“The shape of the update button seems correct, and the spelling and grammar are definitely good enough to get a pass.”
Al-Qudsi does identify some tell-tale signs that the prompt is not all as it seems. A savvy user will know what version of Chrome they are running, in this case version 56, however the prompt has version 53 hard-coded into its dialogue. It also features a rather conspicuous ‘X’ in the top right corner, which gives the game away, according to Al-Qudsi.
However once the file is downloaded, the quality of the scam “takes a nosedive”, with text appearing blurry on prompts, and inconsistent file names for the downloaded material.
Although Chrome will notify the user with a “this file isn’t downloaded very often” warning, it will not catch the download as a malicious file. It also slips by Windows Defender, and a check of virus scanning database VirusTotal reveals that only nine of 59 recorded antivirus scanners are able to correctly identify the file as malware.
Al-Qudsi has forwarded the discovery on to Google’s security team, but pending an update patch, Chrome still fails to identify the file as malware. The firm advises users to be extra vigilant against these types of download prompts.
Pictures courtesy of NeoSmart




So glad you suggest Emisisoft a while ago. So glad I took your advise and have it on my computer.
Thanks for the tip about the Google Chrome ‘Missing Font’ Hack and that EMSISOFT USERS ARE PROTECTED FROM THIS HACK. YAY! thank you Cloudeight.
Thanks for the heads up. I am a font lover but don’t think I would have fallen for it but one’s mind is not always on what it should be!
March 5th, 2017 I have been getting a pop up on some sites that says: Update notifications errorxoo.com Your computer has been blocked error 3658bcyea47b30f . Call us immediately at 855-250-6590. You computer has alerted us that it has been infected with spyware and virus. the following is compromised. FB, credit card number email acc’t and photo. I have emsisoft, and have run scans on this and it does not show any virus or spyward. The only way I can get out of the page it shows up on is by hitting ALT+CTRL+DELETE. Can you tell me what this is all about? Do I have to have my computer looked at to remove this. I have a key ready if I need you to look into this problem. Thanks. Joyce
Joyce,
This is an ad that pops up trying get you to call a number and have your computer “fixed”. Don’t call that number. If Emsisoft is set up with PUPs detection turned off. then you may have (intentionally or unintentionally) installed a browser extension which is causing this, or your network settings have been changed to run a script that causes your computer to be routed to web sites in an unusual way, or it may be the Web sites have been hacked (not very likely), or it may be your HOSTS file has been altered.
If you’re using Chrome, use Incognito mode and try those sites from which you get that popup. You can open an incognito window in chrome by clicking the menu (three vertical dots in the top right-corner) and choosing “New incognito window”. Try browsing using the Incognito window. If you don’t get any of those fake popups (ads), then you’ll know it’s an extension you’ve installed. If that is the case, you should remove any extensions you don’t recognize, then clear Chrome’s history, and restart Chrome.
If you still get the popup ad in incognito mode, it’s not a browser extension – your best bet then would be to schedule an appt with us and let us check over you PC.
Thanks so much.
Best wishes,
TC