 We have been literally besieged with emails from folks who subscribe to other tech newsletters – besides ours — who want to know if a new program created to stop the Cryptolocker ransomware malware, which as featured in newsletters x, y, or z is any good.
We have been literally besieged with emails from folks who subscribe to other tech newsletters – besides ours — who want to know if a new program created to stop the Cryptolocker ransomware malware, which as featured in newsletters x, y, or z is any good.
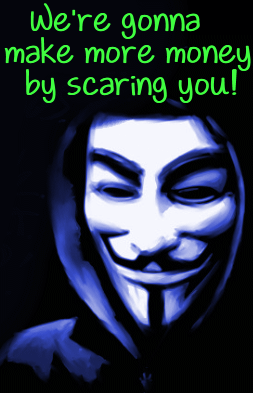
We wrote an article, a while back, about Cryptolocker and in that article we noted that Cryptolocker isn’t new, it’s just the same, old ransomware with a new name and a new modus operandi. These kinds of malicious programs have been around for a decade, but leave it up to visitor-hungry Web sites and subscriber-thirsty newsletters to sensationalize for no other purpose than to scare readers and attract attention. If you read some newsletters, you would think that Cryptolocker is brand new – and the worst malware to ever hit the Web and you can hardly avoid getting it. But folks, these newsletters know better. They just want more visitors and more subscribers, because that means more money for them. And there is nothing wrong with expecting to be paid for your time. It’s not malevolent to make a profit, but profiting from scaring people and fear-mongering is just plain wrong.
When we discussed Cryptolocker, we tried to make it very clear that as with most other malicious software, your best defense is your brain and your common sense. Cryptolocker (like the many other variants of ransomware over the years) spreads through user carelessness; people infect their computers by opening attachments when they don’t know what the attachment is or they’re not certain they even know who sent it; clicking links in email from people or places they don’t know; clicking links on compromised Web sites, and falling for scam ads that promise to speed up or which find loads of viruses and Trojans on their computer (none of which exist), then offering to clean them up.
Installing the program featured lately in many tech newsletters, may well fend off Cryptolocker, but no better than you could do but just stopping to think before you click. It’s an unnecessary crutch you don’t need, though it may work as described. If you keep using crutches to walk, eventually you won’t be able to walk without them.
You can load your computer down with all manner of anti-spyware, anti-malware, anti-virus, anti-phishing, anti-hacking programs, but not one of these is necessary if we all just used common sense, slowed down and use the software God installed between our ears.
No, we’re not recommending that you not use a good Antivirus program, nor are we saying you shouldn’t use a firewall. These are good backups to your brain and your common sense. But to install a program designed to stop just one thing — Cryptolocker, is unnecessary. Installing unnecessary programs is just cluttering your computer and who knows what kinds of software conflicts installing specialized software may cause with your regular security programs.
Some antivirus / anti-malware programs already, as a matter of course, provide protection, not only from Cryptolocker, but from most of the other ransomware from which Cryptolocker evolved. Emsisoft, is one anti-malware / antivirus we know of, that protects you from Cryptolocker and the other ransomware floating around out there. There are probably others as well.
We would love more Web site traffic; we would love more subscribers. But we refuse to assume a sensationalistic posture just to acquire more visitors or more subscribers. Sensationalism is a form of prevarication. It’s hard to believe the editor of a tech newsletter would ever download and install a program created which has but one purpose. And if he or she wouldn’t install it, why would they recommend it to their readers? Can you guess?
We will continue to give you the truth and the best possible advice regardless of the number of visitors or subscribers we have. We want you to trust what we say and teach you to think logically. Our best advice is:
- Install a good antivirus / anti-malware like Emsisoft
- Always use the latest version browser available (Chrome, Firefox, or if you must, Internet Explorer)
- Do not click links in email unless you know who sent you the email.
- NEVER EVER OPEN ATTACHMENTS IN EMAIL UNLESS YOU ARE 100% POSITIVE YOU KNOW WHO SENT IT, WHAT IT IS, AND YOU WERE EXPECTING IT.
- SEE NUMBER 4
- Never Panic
- Don’t rush – take your time and think before doing
- Take your common sense with you on the Web and use it 100% of the time
Don’t count on software to protect you 100% of the time against 100% of all malicious programs; it’s an imperfect world, an even more imperfect Web, and not a single perfect program exists anywhere.
We want to help keep you safe. And if you follow the steps above, you will never get Cryptolocker or any other ransomware. You don’t need no stinkin’ special software to protect you against Cryptolocker… you just need your common sense and your brain.


Again, you have given us the honest truth. I will always keep my faith and trust in your newsletter and look to it for sound guidance. Thank you for all that you continue to do for us out here in computer land.
Just wanted to repeat what Jean said above … that once again, you have given us the truth and sound guidance with this problem (the Cryptolocker ransomeware) as with all others. I absolutely had succumbed to complete panic about this malware and was ready to install a program that would save our computer from this most recent computer evil. Thank you so much for helping us ‘keep calm and carry on’ and rely on our own wits and logic (and and Emsisoft!) to get us through these times. But most of all, thank you, each and every day, for you!
I love you two. It’s a relief to see your common sense KISS (Keep it simple, Stupid!) articles reminding people that in many ways you’re on your own here in cyberland so think before you act. If you can remember that and keep a repair key for Cloud8 handy you will be fine.
Me? I’ve got 3 repair keys. So far, I’ve been lucky and not had to use ’em which is a good thing. But if I ever get stupid I’ve got a good life preserver handy.
Your advice not to open any email link from anyone you don’t know is good but sometimes, even someone you know might unknowingly pass a virus on to you so everyone should still be very careful clicking on any link that they might not be familiar with and thanks for the info about this ransomware.
So what you are saying is that everyone else is out of step except for you, including renowned experts such as Brian Krebs and Lawrence Abrams.
To state unequivocally that people do not need a “special” program to help protect against Cryptolocker is a dangerous generalization. Trouble is; you can tell people not to open email attachments from unknown or unverified sources ad nauseam… some (plenty) still don’t heed the advice.
Your explanation of CryptoLocker is also misleading. Sure, ransomware has been around a long time but this particular variant (CryptoLocker) is much more dangerous; it’s more advanced, more widespread, and the encryption almost impossible to overcome.
I might also point out that most FREE AVs do not protect against the CryptoLocker infection. Some will remove the infection after the fact but by then the encryption has already been applied and the damage well and truly done.
CryptoPrevent, the software specifically designed to block CryptoLocker, is portable and extremely lightweight, using very little, if any, resources. I can see absolutely no reason why people should not use it to help protect against the CryptoLocker infection. No-one is immune from making an occasional mistake and clicking on the wrong thing, without any dedicated protection the results could be catastrophic.
Bottom line; CryptoPrevent cannot possibly hurt and may very well save a lot of heartache.
It’s kind of amusing what you say. These so-called security experts you cite? How many companies and governments have security experts on their payroll — and how many hackings do we have every month? Hundreds. So if these so-called experts are so damned smart, why are the hackers and cyber-criminals oftentimes smarter? It’s because people are careless and people are trusting. Too many people click links they shouldn’t click. Too many people install software without reading the installation dialogs — they just click next, next, next, finish. You can stick as many security programs and firewalls on a computer as you want — and you can hire all the experts you want, and it’s not going change one single thing. It never has. People are careless. Smart people in the real world, sometimes forget to take their brains along when the go online. People are too trusting. In the real world they question things, they use common sense, they know if something seems to be too good to be true, it usually is. But, for whatever reason, when they get on the Internet, they throw their common sense out the window; they throw caution to the wind.
So called security experts wouldn’t make a dime if they couldn’t scare people and create a market for their “services”. Anyone can be an expert. All they have to do is say they are — and there a lot of “experts” on the web who are experts only because they say they are. And people are trusting, remember? Again, I say: if these security experts are so expert then why are so many financial, corporate and government computers hacked every day. Are the hackers more expert than the experts? The U.S. government is finally getting smart and hiring cyber-criminals and hackers as security consultants — as well they should. They are proven experts, right? Security experts have failed to protect government and corporate databases and Web sites from hackers. Corporations and governments pay millions to so-called security experts, and yet the bad guys win far too often.
As far a cryptolocker being new, it isn’t. Cryptoviral extortion has been around since since at least 2004. You can research cryptoviral extortion, if you’d like. Just because you wish Cryptolocker was new, doesn’t mean it is. Cryptolocker is a new singer but it’s singing a song that’s 9-years-old.
Finally, you conclude “Bottom line: CryptoPrevent cannot possibly hurt and may well save a lot of heartache.” All I can say is you must be the author of CryptoPrevent. You will excuse if question your altruism. There is no benefit to be gained by scaring people and name-dropping (security experts) as if this lends your comments some sort of credence. If these so-called security experts were so good, they wouldn’t be continually out-smarted by cyber thieves and twelve-year-old hackers (see this video of the young hacker)
You have an agenda, Krebs wrote an article hailing CryptoPrevent as something everyone needs. We say everyone doesn’t need it but we never said people shouldn’t have security software installed – hopefully security software good enough to prevent Cryptolocker — not a uni-tool like CryptoPrevent. By your logic, people should install a special software program for every ransomware – whichever one happens to make the rounds. We don’t think one pill, one disease, is a good approach. B
Your logic is flawed and your agenda is transparent. I would have deleted your post as I think you’re trying to promote CryptoPrevent on this site, except I thought people would like to read it, as well as my reply.
There is no nepenthe when it comes to be safe online. There is no software panacea that will prevent every single threat from attacking a computer. There is no solution that works 100% of the time, against 100% of the threats users face each time they connect to the Internet, that works for 100% of the people, 100% of the time.
The point we were making (and you well know this – you don’t write like a stupid person) is that knowledge and caution and common sense are the first line of defense. Of course we recommend everyone install a good antivirus, use a firewall, and use a good antimalware. We don’t recommend uni-tools like CryptoPrevent, and that’s what you wanted to promote.
But our readers don’t know Brian Krebs from Maynard G. Krebs our readers don’t know Lawrence Abrams from Abraham Lincoln and that’s fine. Krebs and Abrams are going to protect them from squat. Common sense, knowledge and caution are the first line of defense.