Wednesday Newsbytes: Windows 10 22H2 and Windows 12, Google Maps New Time Travel Feature, UEFI Rootkits, the End of the Leap Second, and more…
Every day we scan the tech world for interesting news in the world of technology. Every Wednesday, we feature some news articles that grabbed our attention over the past week. We hope you find this week’s ‘Wednesday Newsbytes’ informative and interesting!
Windows 10 22H2 could save you from the tyranny of Windows 11
Hate Windows 11? Windows 10 22H2 could arrive soon, instead
More evidence has emerged that Windows 10 will be getting a major update, known as 22H2, and that’s great news for people who would want to stick with the older operating system, rather than upgrade to Windows 11.
As Windows Latest reports(opens in new tab), references to Windows 10 22H2 have been spotted in a recent update, KB5015684. This update is currently with Windows Insiders, who are testing it before it gets rolled out to everyone using Windows 10…
Windows Latest installed the update, and despite the version number changing to 22H2, it appears this is a minor update with only a few behind-the-scenes changes…
Analysis: Windows 10 isn’t dead yet
The revelation that Windows 10 is getting a 22H2 is good news for anyone who doesn’t want to upgrade to Windows 11, or anyone who simply can’t, due to the newer operating system’s rather complex system requirements.
Despite Microsoft pushing people to upgrade to the new OS, and with hype building for Windows 11 22H2, which is shaping up to be a major update that brings a lot of new features – many of which people have been clamoring for – it’s good to see that Windows 10 isn’t being forgotten about.
This is especially true as rumors swirl around the possibility of Microsoft launching Windows 12 (emphasis added by Cloudeight) as soon as 2024. Microsoft has promised to continue to support Windows 10 until its ‘end of life’ on October 14, 2025, and it looks like it’s sticking to its word.
Google Maps Now Lets You See What Your House Looked Like Years Ago
Google, in celebration of Street View’s 15th anniversary, has updated its tool with an exciting new feature: time travel.
Since 2007, the mapping technology has allowed users to explore the world through street-level photography. Now, users can browse the same places but at different intervals in the past — specifically, the times when the Street View car had passed through the area.
For instance, the photos below show Little Island in NYC. The first picture was taken in 2014, and the other in 2021. What’s interesting is that this update unintentionally creates a location’s before-and-after. Just look at the photos of Pier 55, the difference is night and day!
The tool can be used not only to see famous attractions and landmarks but also to reminisce about places that are more personal to you. In my case, it was amusing to see how my house and neighborhood have changed over the years. So nostalgic!
And for more practical matters, you could use it to compare choices and influence your decision-making process. For example, if the decision to paint your front door another color had aged well. Or, if you’re planning to buy or sell, to compare the development of the area from a decade ago to now.
To use the time travel feature, carry the tiny yellow person from the lower right-hand corner and drop him onto the map. This will activate Street View, and you should see a tiny clock icon on the top left corner. A slider will appear with various dates, and you can move the bar to travel through time.
Read more at Apartment Therapy
Discovery of new UEFI rootkit exposes an ugly truth: The attacks are invisible to us
Turns out they’re not all that rare. We just don’t know how to find them.
Researchers have unpacked a major cybersecurity find—a malicious UEFI-based rootkit used in the wild since 2016 to ensure computers remained infected even if an operating system is reinstalled or a hard drive is completely replaced.
The firmware compromises the UEFI, the low-level and highly opaque chain of firmware required to boot up nearly every modern computer. As the software that bridges a PC’s device firmware with its operating system, the UEFI—short for Unified Extensible Firmware Interface—is an OS in its own right. It’s located in an SPI-connected flash storage chip soldered onto the computer motherboard, making it difficult to inspect or patch the code. Because it’s the first thing to run when a computer is turned on, it influences the OS, security apps, and all other software that follows.
Exotic, yes. Rare, no.
On Monday, researchers from Kaspersky profiled CosmicStrand, the security firm’s name for a sophisticated UEFI rootkit that the company detected and obtained through its antivirus software. The find is among only a handful of such UEFI threats known to have been used in the wild. Until recently, researchers assumed that the technical demands required to develop UEFI malware of this caliber put it out of reach of most threat actors. Now, with Kaspersky attributing CosmicStrand to an unknown Chinese-speaking hacking group with possible ties to cryptominer malware, this type of malware may not be so rare after all…
Meta calls for the death of the leap second
It devastates the tech industry every time it happens, Meta says.
Meta is putting its considerable weight behind the tech industry’s push to do away with the leap second. In a post on the company’s engineering blog, Meta production engineer Oleg Obleukhov and research scientist Ahmad Byagowi talked about how a leap second can wreak havoc on a network, along with the solution Meta implements to prevent outages and any issues it could cause.
The leap second was introduced back in 1972 as a way to adjust Coordinated Universal Time (UTC) and make up for the difference between the International Atomic Time (TAI), which is measured by atomic clocks, and imprecise observed solar time (UT1). They sometimes don’t match due to irregularities and slowdown in the Earth’s rotation caused by various climate-induced and geological events, such as the melting and refreezing of ice caps on the tallest mountains.
As Obleukhov and Byagowi note, the offset a leap second creates can cause issues all over the industry. In 2012, for instance, it took Reddit out for 40 minutes when the time change confused its servers and locked up its CPUs. A time leap added in 2017 also affected Cloudflare’s DNS service.
To prevent unwanted outages, Meta and other tech companies, such as Google and Amazon, use a technique called ‘smearing.’ These companies ‘smear’ a leap second by slowing down or speeding up the clock throughout a number of hours. Meta smears a leap second throughout 17 hours, while Google uses a 24-hour smear technique that lasts from noon to noon and encourages everyone to follow suit. That way, a leap second doesn’t create any weird time stamps that could throw networks off.
But Meta isn’t advocating for the adoption of its smearing technique…
Private browsing may not protect you as much as you think
For years, the most popular internet browsers have included options to search for and visit websites in ‘private’ modes. Those options may now be viewed as vital tools for some in the wake of Roe v. Wade’s demise, as abortion-seekers look to avoid having their personal data used against them in states where abortion is criminalized.
But clicking the ‘private’ browsing option might not protect you as much as you think, some privacy experts say.
These options have different names — Private Browsing on Safari and Firefox, and Incognito mode on Chrome — but the functionality is similar on each. In these private modes, the chosen browser does not keep a log of sites visited, cached pages, or saved information like credit card numbers and addresses. It also prevents information from sessions from being stored in the cloud.
Although using these options does add a certain level of protection online, privacy experts say it stops short of preventing the user from being tracked altogether — potentially limiting the protections it may afford women in this new legal landscape.
‘We have to recognize that oftentimes simply toggling on a private mode does very little to prevent third-party tracking and especially law enforcement tracking,’ said Albert Fox Cahn, founder and executive director of the Surveillance Technology Oversight Project and a fellow at the New York University School of Law.
What does private browser mode do?
As designed, private browsing modes are best suited for protecting your web activity from other people who use the same device, according to experts, but it does little beyond offering that local shield…
For related info see this page
Anti-Vaxxers Looking for Love Had Their Data Exposed
A dating app for the unvaccinated, Unjected, left user data totally unprotected, according to new research.
These days, if you’re single and ready to mingle, there are a wealth of dating apps to choose from—depending on what you’re looking for. For one-night stands, there’s Tinder; for respectful brunch dates, there’s Bumble; and for people who believe in both, there’s Hinge. Oh, but don’t forget Unjected—a dating app for the unvaccinated that also lets you donate your blood and breastmilk (????).
According to a new report, another unintended feature of this anti-vax site has been that it shares your data with the internet. Until recently, a giant security hole allegedly sat unfixed on the website, allowing anyone with the know-how to sneak onto the platform and steal or change information.
The Daily Dot was the first to note that Unjected appeared to have a massive security problem on its hands. According to the outlet, a web researcher who goes by GeopJr discovered that the site’s administrator feature was missing basic security and authentication protections. GeopJr says that the site’s administrator dashboard, which allows a person to add or edit user profiles and the site’s webpages, was left totally open to the internet because the site hadn’t been taken out of “debug mode.” Climbing into the admin seat, a cybercriminal could basically steal and edit information from the site at will…
Thanks for reading this week’s Wednesday Newbytes. We hope you found these articles informative, interesting, fun, and/or helpful. Darcy & TC


What should we worry about most? The Private Browsing article mentioned above or https://ussanews.com/2022/07/19/does-facebook-have-your-medical-records/
We sure are just GIVING our privacy away in many many ways. SAD!
Hi Muriel,
I think by now everyone knows Mark Zuckerberg didn’t become a gazillionaire from ads on Facebook. User information is gold on the Internet. Google learned it well, but Facebook takes it to another level. Anyone who chooses to use Facebook has no expectation of privacy -and anyone who believes they do will someday get a rude awakening. We just don’t trust Facebook at all anymore.
But any other social media you may choose does not exist to keep you in touch with friends and family – they exist to make money. Selling personal information is like being able to print money.
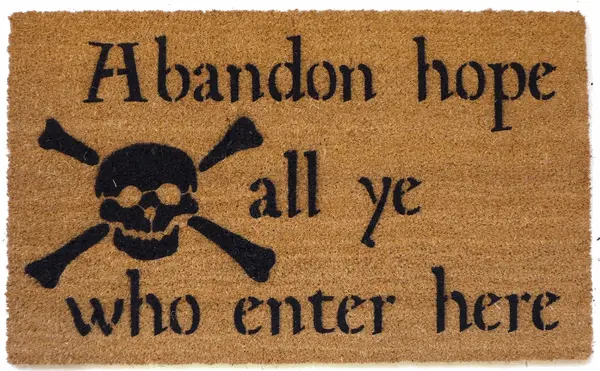
This should be posted on the front page of all social media sites as their simplified privacy policy…